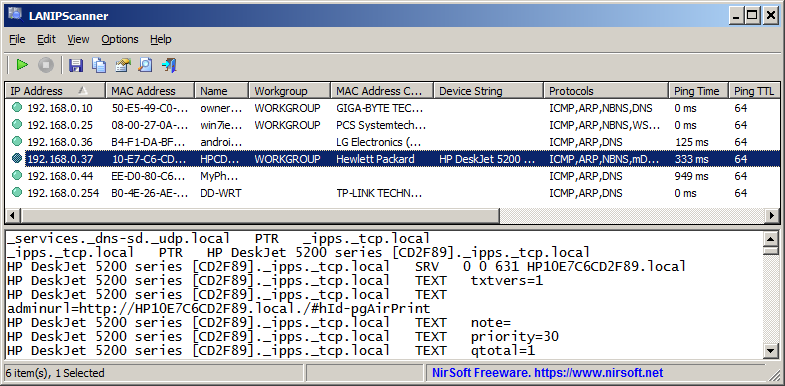
LANIPScanner is a new tool for Windows that scans your network and displays the list of all computers and devices that are currently connected to your network. LANIPScanner uses multiple network protocols to scan your network, including ICMP (ping), ARP, mDNS, DNS, NBNS, SSDP.
For every computer or device that is connected to your network, the following information is displayed (Only if it’s available): IP Address, MAC Address, MAC Address Company, Device Name, Workgroup, Device String, Ping Time, Ping TTL, Device Type, Protocols List, IPv6 Address, IPv6 Link Local Address.
When a device responses to SSDP or mDNS protocol, you can also view the raw data received from the device in the lower pane, by selecting the device in the upper pane.
The LANIPScanner tool works on any version of Windows starting from Windows XP and up to Windows 11. Both 32-bit and 64-bit systems are supported.
You can download the new LANIPScanner tool from this Web page.