msn-blocked.com and msnpass.info are a pair of scam Web sites in french that are extermly active in the last few weeks.
The first one, msn-blocked.com – asks innocent users to type their MSN user/password, and then floods all their contacts with fake instant messages that invite them to join msn-blocked Web site, and enter their user/password too.
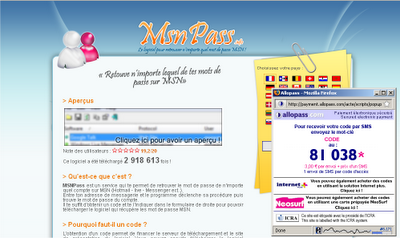
The second one, msnpass.info – offer the users of msn-blocked.com to purchase the MessenPass utility of NirSoft through the SMS payment system of allopass.com, misleading french users that don’t know that this utility is available for free at www.nirsoft.net.
As I already reported in my previous posts, these Web site were hosted in ovh.net hosting company, but in the last few days the owner of these scams moved most of the servers into another hosting company – EURO-WEB Servers renting, which is also an hosting company in France. Although most of the activity moved to the new hosting company, some of the servers are still active in the previous hosting company – ovh.net
The host names in the new hosting company are:
a.msnpass.info
b.msnpass.info
c.msnpass.info
d.msnpass.info
e.msnpass.info
f.msnpass.info
a2.msn-blocked.com
b2.msn-blocked.com
c1.msn-blocked.com
d1.msn-blocked.com
f5.msn-blocked.com
…And there are possibly more…
Ridiculous Answer From Allopass.com
I the previous post, I reported that there was no answer from Allopass payment company that is used as a part of msnpass.info/msn-blocked.com scam.
So after a while, they sent me their ridiculous answer to my complaint about these scams, and here’s the quote from their response:
“Please apologize for this late answer. As a payment system provide, Allopass is not entitled to take side in this kind of dispute. However, we just notified the publisher of http://www.msnpass.info/ of your complaint, and now look forward to his reply.“
So Allopass don’t want to “take side” in this issue, but they actually enjoy to take their side in sharing the revenue with msnpass.info owner.
Each time that a new innocent victim pays for my MessenPass software in msnpass.info Web site, Allopass company also get their side in the SMS revenue, together with msnpass.info scam owner.
But the main problem with msnpass.info is not the action of illegally selling NirSoft software, but the fact that this Web site get all the traffic by spamming the MSN Messenger accounts of innocent people with fake messages generated by msn-blocked.com Web site.
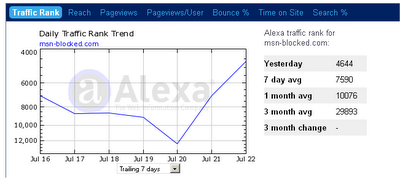
As you can see from Alexa ranking, the traffic of msn-blocked.com Web site continue to grow, and in the last days the it reached to a new record:
most of the traffic of msn-blocked.com comes from countries with french speakers – France, Belgium, Switzerland, and a few more.
How This Scam Works
If you still don’t understand how exactly this scam works, and how these scam Web sites get so much traffic, here’s a simple explanation of the viral spreading made in these Web sites.
For the examples below – User X, User Y, and User C are french speakers that constantly use MSN or Live Messenger to chat with their friends.
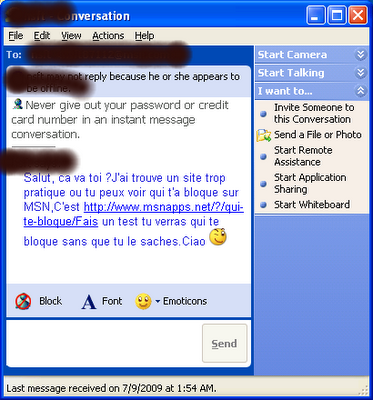
- User X get an instant message in MSN from his good friend, User Y, that recommend him to visit msn-blocked.com Web site (And User X doesn’t know yet that this is fake message generated by msn-blocked.com Web site)
- User X Visit msn-blocked Web site and put his MSN user name and password, assuming that it’s a safe Web site, because User Y, his good friend that he trust, sent him to this site.
- After giving his MSN user name/password to msn-blocked, this Web site connect to the MSN account of User X, and send fake instant messages to all his contacts !!
- Now User C, D, E, F, and others, which are in the contacts list of User X, receive the fake invitation message from User X, and some of them, like User X, do the same mistake, and go to msn-blocked Web site and give their user name/password.
- In the User X side, msn-blocked page is loaded and display his contacts list for a few seconds.
- After a few seconds, the Web site is suddenly redirected to www.msnpass.info Web site.
- www.msnpass.info Web site offers User X to download my MessenPass Software by using the SMS payment system of allopass.com
User X still doesn’t know that all his contacts received the fake instant messages in his name, and he think that msnpass.info is good Web site recommended by his friend, and of course, User X doesn’t know that MessenPass utility is available to download for free at NirSoft Web site. - User X send an SMS and get the code for downloading my MessenPass Software, assuming that User Y recommeneded him to do so.
- When User X send the SMS, the payment is shared between the scam owner, Allopass payment company, and the phone company.
- After a while, User C, a friend of User X, ask him about the link he sent him earlier.
User X doesn’t remember that he sent any link to User C, and he start to understand that msn-blocked.com sent fake messages to all his contacts.
But it’s already too late. Some of the User X contacts, the received the same fake invitation message, already gave their MSN user/password, and continued the viral spreading of msn-blocked scam. - User X, angry about the embarrassment that this Web site caused him, browse into msn-blocked.com link again, and report it as ‘Web Forgery’ from the Web browser interface.
After a while, the Web address reported by User X will be blocked by Firefox/Google and other Web site blockers, but it won’t help much to the next victims, because the scam owner constantly modifies the Web site address. For example: If User X, received the Web site address as s12.msn-blocked.com, the next victims will get a new address like s35.msn-blocked.com, and thus it won’t be blocked for the next victims. - The owner of mspass.info and msn-blocked sites, accumulates more and more money from the SMS system, allowing him to pay more for the hosting services and to extend his scam Web sites to more servers.
- Due to the nature of “viral spreading” like in this scam, the number of users visit these sites grows exponentially, and the scam owner rent more and more servers in order serve all the site “visitors”.
The scam owner probably relies on payments from Allopass system for paying the new hosting servers. - Allopass company also enjoy the scam of msnpass.info, and get their part of the revenue, without caring about the nasty way that the visitors are sent into msnpass.info Web site, and without caring about violation of my intellectual property rights, even if it’s against their own conditions of use.
- It’s possible that all MSN user/passwords provided by users in msn-blocked Web sites, are collected into a large database of passwords for using it later for
identity theft and other crimes.
That’s all for now.
You are welcome to add your comment about Allopass behaviour in this matter, and whether they should continue to provide their payments services for the nasty scam Web sites that I described above.

The MAZZTer says:
I am sure if Google receives enough reports about different msn-blocked subdomains they will eventually block the whole domain. If the individual persists with different sites Google may block the web hosting service entirely, if it hosts a number of illegitimate websites.
July 25, 2009, 6:55 pm- says:
You really should report Microsoft about this scam website. Microsoft really doesn't like scammers that use their trademarks.
July 26, 2009, 6:38 ameduardo says:
eduardo_borges_19@hotmail.com
August 21, 2009, 2:59 pmscam says:
Be aware of Domainsponsor scam company. This company operates under domainsponsor and oversee names and washes money via oversee company. Tax fraud and cheating is what they do. Stay away from them. Classaction lawsuit is coming.
September 12, 2009, 5:30 pmVaffangool says:
Anyone who uses such services every day should have an intuitive sense of how these things work. Every person spammed in the first round should be aware that their friend has been compromised and did something stupid with his contact list. Obviously, not everyone is as savvy as they ought to be–and the problem is even worse with these Web2.0 B2B’s. The executives who run these companies cannot tell the difference between obvious scams and legitimate businesses–and they will never entrust their IT guys with potentially costly decisions.
That leaves them dependent on user reports. It’s a slow-moving process, but once the inertia is overcome, they eventually make the right decision. In the meantime, the scammers steal your IP and damage your reputation in the process. I would suggest you include a message in your installers that makes it clear that your applications are freeware–and the user should demand a refund if he was charged money for the program.
At least you know you’re in good company–other freeware programs that have been sold by the unscrupulous to the unwitting include VLC and uTorrent.
January 20, 2013, 4:38 pm